You spent millions securing production
Your Test Environments Have None of It.
That’s where your next satisfactory audit finding, or your next breach, is coming from.
The Uncomfortable Truth
About Your Test Environments
Production data is often copied, unmasked, into less secure test environments.
![]() What we typically find:
What we typically find:
Non-production holds 3–5× more sensitive data than production — with a fraction of the controls. Every copy is a breach surface.
![]()
Full production copies in 4–7 environments
Each with unmasked PII
![]()
Developers with unrestricted access
To real customer records because “they need realistic data”
![]()
No policy on data lifecycle
How long test data lives, who accesses it, or when it’s purged
![]()
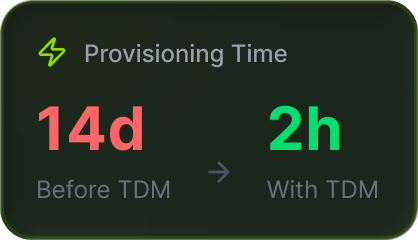
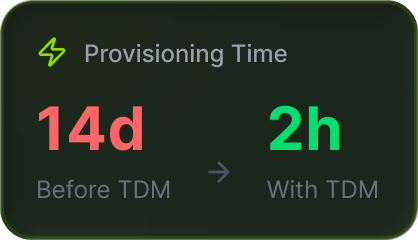
Environment provisioning
Taking 5–14 days per sprint cycle
![]()
Complete TDM Stack for
Regulated Enterprises
From profiling to purging — every capability you need for compliant test data provisioning.
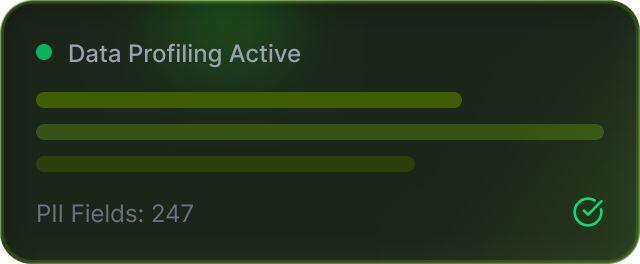
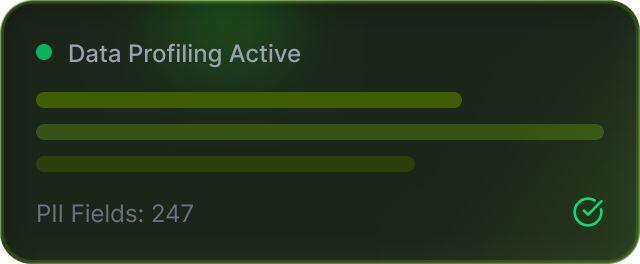
Analyse source databases to map data types, sensitivity classifications, and dependencies before any transformation.
![]() THE DIGITRALY DIFFERENCE
THE DIGITRALY DIFFERENCE
We classify every field against GDPR, HIPAA, PCI DSS and produce a masking policy map before transformation
Extract referentially intact portions of production databases at 5–10% of original volume. A 10TB database becomes a 500GB test dataset that covers scenarios better because it’s curated, not cloned.
![]() THE DIGITRALY DIFFERENCE
THE DIGITRALY DIFFERENCE
Rule-based extraction preserving foreign keys, business logic, and edge cases. Faster refreshes. Lower storage.
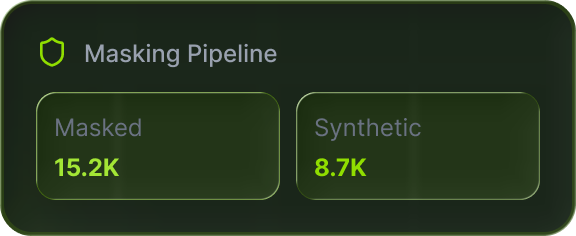
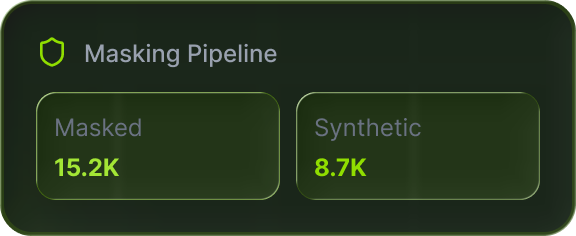
Replace PII, PHI, and financial data with realistic fictitious values. Static masking for persistent environments. Dynamic masking for real-time, role-based access control.
Common failure: Masking names and emails but leaving DOB, postcodes, and transaction patterns intact — enough to re-identify individuals.
![]() THE DIGITRALY DIFFERENCE
THE DIGITRALY DIFFERENCE
Masking as an automated pipeline, not a one-time project. Schema changes trigger policy updates. Every run is logged and auditable.
Analyse source databases to map data types, sensitivity classifications, and dependencies before any transformation.
Use when: Production access is restricted, edge cases don’t exist in production, load testing needs millions of records, or you’re building products where production data doesn’t exist yet.
![]() THE DIGITRALY DIFFERENCE
THE DIGITRALY DIFFERENCE
Synthetic pipelines producing datasets that pass production validation rules. Format-correct, distribution-accurate, audit-documented.
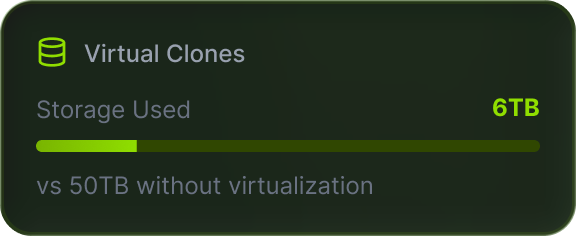
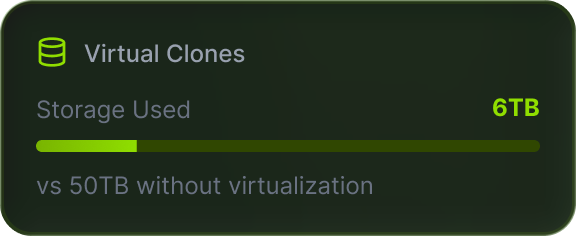
Thin, writeable clones of multi-terabyte databases without duplicating storage. 10 teams × 5TB = ~6TB total instead of 50TB. Provisioning drops from days to minutes.
![]() THE DIGITRALY DIFFERENCE
THE DIGITRALY DIFFERENCE
Virtual database provisioning integrated into CI/CD — every build triggers an automated, masked, right-sized clone.
Policy-driven, auditable deletion of data past its retention lifecycle. GDPR right-to-erasure, HIPAA retention rules, and PCI DSS storage limits all mandate it — including in test environments.
![]() THE DIGITRALY DIFFERENCE
THE DIGITRALY DIFFERENCE
Automated purge workflows with full audit trails, integrated with data governance tooling. No forgotten environments.
![]()
Practical Cybersecurity
Without Compromise

Automation, not projects
We build CI/CD-integrated pipelines that provision compliant test data on demand. No DBA bottleneck.
Profiling first.
We always start with profiling to scope based on your actual environments, not assumptions.
Practitioners, not resellers.
We implement strategies across all major enterprise TDM platforms, open-source, and cloud-native solutions. We recommend what fits your architecture— not what pays us the highest margin.

Regulated-
industry depth
Aviation passenger data. Banking transactions. Healthcare PHI. We’ve worked where one unmasked field triggers a regulatory finding.
Regulated Industries We Serve
Tailored solutions where data security is existential, not optional.
![]() Airlines & Aviation
Airlines & Aviation
PNR masking, loyalty data subsetting, PSS test environments, IATA compliance
![]() Banking & Fintech
Banking & Fintech
PCI DSS masking, SOX-auditable purging, transaction synthesis, core banking virtualisation
![]() Healthcare
Healthcare
HIPAA PHI masking, synthetic patient data, EHR subsets, HL7/FHIR-compliant pipelines.
![]() Insurance
Insurance
Policyholder anonymisation, claims virtualisation, actuarial synthetic datasets.
![]() Telecom
Telecom
CDR masking, subscriber subsetting, MVNO test provisioning.
![]()
Our engagement model
A structured, phased approach from assessment to production-ready automation.
PHASE 1 Weeks 1-3
Discover & Profile
- Map non-production environments
- Profile schemas and classify sensitive fields
- Produce sensitivity heat map and masking blueprint
PHASE 2 Weeks 3-5
Design
- Define subsetting rules and masking policies
- Set synthetic requirements and virtualisation targets
- Configure purge schedules
- Deploy tooling and build automated pipelines policies
- Integrate with CI/CD
- Configure self-service provisioning
- Monitor compliance and enforce retention
- Re-profile after schema changes
- Right-size continuously
All You Need to Know
Frequently Asked
Questions
TDM is the practice of provisioning, securing, and governing non-production data. It combines data profiling, subsetting, masking, synthetic data generation, virtual databases, and purging to deliver compliant, right-sized test datasets on demand.
Replacing sensitive data (PII, PHI, financial records) with realistic fictitious values so test environments function without exposing real individuals. Mandatory under GDPR, HIPAA, PCI DSS.
Masking transforms real data by obfuscating sensitive fields. Synthetic data is generated from scratch with zero connection to real individuals. Use masking when production data is accessible; synthetic when it’s restricted or edge cases are needed.
Profiling identifies data types, sensitivity, relationships, and quality issues. Without it, you mask wrong fields, break subsets, and generate unrealistic synthetic data.
Thin, writeable database clones without duplicating storage. Teams get isolated copies in minutes, cutting infrastructure costs up to 90%.
Extracting a referentially intact, smaller portion of production — typically 5–10% of volume — while preserving foreign keys and business logic.
In regulated industries, yes. GDPR right-to-erasure, HIPAA retention rules, and PCI DSS storage limits all require auditable deletion — including in test environments.
TDM pipelines plug into CI/CD. Builds auto-trigger masked, right-sized datasets or virtual clones — eliminating DBA tickets and multi-day waits.
Tool-agnostic. We work with all major enterprise TDM platforms, open-source frameworks, and cloud-native solutions – recommending based on your architecture, not vendor partnerships.
10–14 weeks. Discovery (2–3 weeks), strategy (2 weeks), implementation (5–7 weeks), then ongoing governance.
